The Problem VLANs Solve
Imagine a company with 200 employees: Finance, HR, Engineering, and Guest WiFi all sharing the same physical network switches. Without segmentation, a broadcast sent by any device reaches every other device. A compromised guest laptop can attempt connections to financial servers. HR data crosses the same wire as engineering traffic. The network is a flat free-for-all.
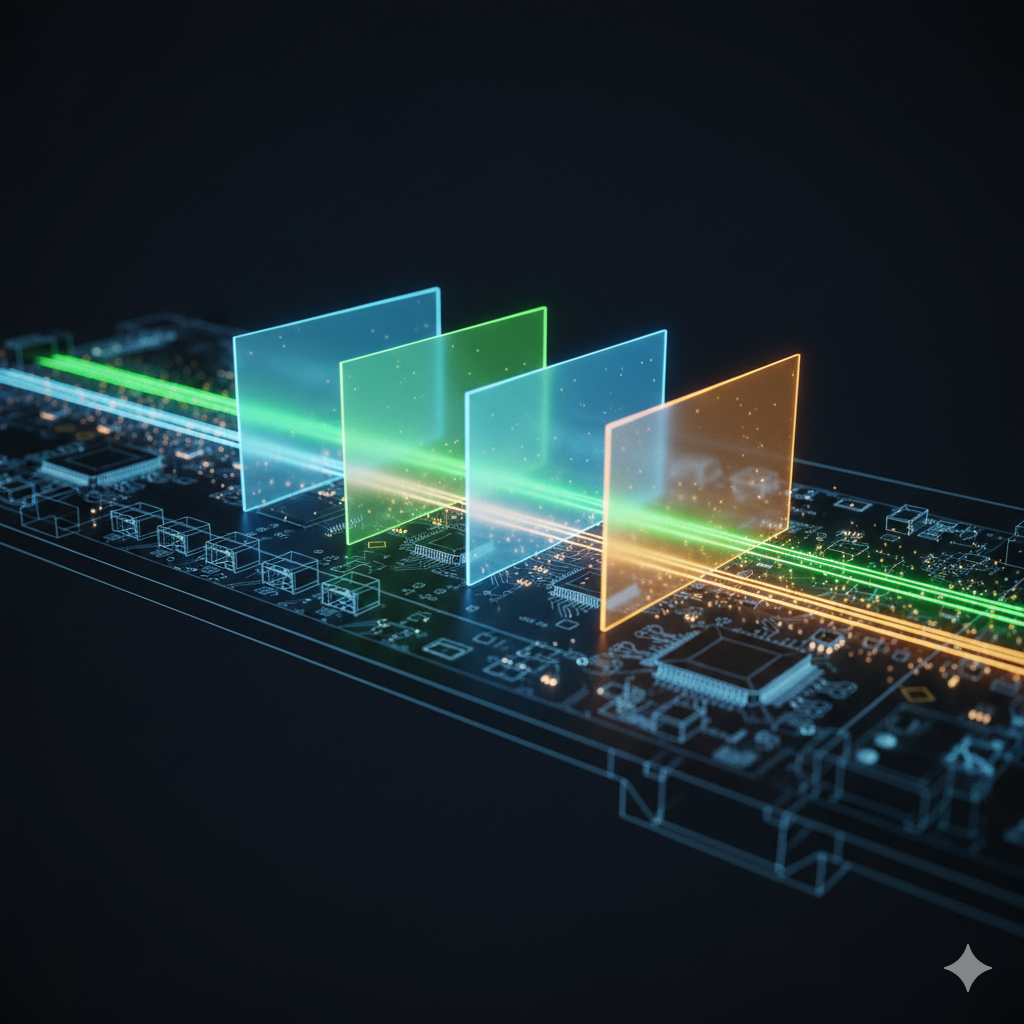
VLANs (Virtual Local Area Networks) solve this by creating logical separation on top of physical infrastructure. VLAN 10 carries Finance traffic. VLAN 20 carries Engineering. VLAN 100 carries Guest WiFi. Devices in different VLANs cannot communicate directly — as if they were on completely separate physical switches — even though they share the same hardware.
How 802.1Q Tagging Works
The IEEE 802.1Q standard defines how VLAN information is carried in Ethernet frames. When a switch marks a frame as belonging to a particular VLAN, it inserts a 4-byte tag into the Ethernet header. This tag contains a 12-bit VLAN ID, supporting up to 4,094 unique VLANs (IDs 1 and 4095 are reserved).
End devices — computers, printers, phones — are generally unaware of VLANs. They send and receive normal untagged Ethernet frames. The switch handles the tagging behind the scenes.
Access Ports vs Trunk Ports
This is the most important operational concept in VLAN configuration.
Access ports connect to end devices. They belong to exactly one VLAN. Frames arriving on an access port are untagged — the device doesn't know about VLANs. The switch assigns the frame to the configured VLAN internally and strips the tag when forwarding back to the device. Configure a port as access when it connects to a PC, printer, IP phone, or access point (for single-SSID deployments).
Trunk ports carry traffic from multiple VLANs simultaneously. They're used between switches, between a switch and a router, or between a switch and a firewall. Frames on a trunk port are 802.1Q-tagged so the receiving device knows which VLAN each frame belongs to. Configure a port as trunk when it needs to carry more than one VLAN.
Inter-VLAN Routing
VLANs are isolated at Layer 2. For devices in different VLANs to communicate, traffic must pass through a Layer 3 device — a router or a Layer 3 switch.
The classic approach is a router-on-a-stick: a single router interface connected to a trunk port on the switch, with sub-interfaces configured for each VLAN (each sub-interface has its own IP address acting as the default gateway for that VLAN). Traffic from VLAN 10 destined for VLAN 20 leaves the switch trunk port tagged, arrives at the router, gets routed, and returns tagged with VLAN 20.
The modern approach is a Layer 3 switch with Switched Virtual Interfaces (SVIs) — one logical interface per VLAN, all routing done in hardware at wire speed. This is what enterprise networks use. The router-on-a-stick is fine for small deployments; Layer 3 switching is essential at scale.
Native VLAN — A Security Consideration
On trunk ports, 802.1Q defines a "native VLAN" — the VLAN whose frames are transmitted untagged. By default on Cisco switches, this is VLAN 1. This creates a security risk: if both ends of a trunk have VLAN 1 as native, an attacker with access to a switch port configured as VLAN 1 may be able to inject untagged frames that traverse trunk links undetected.
Best practice: change the native VLAN to an unused, non-routable VLAN (e.g., VLAN 999) on all trunk ports. This is a standard hardening step and appears on most security benchmarks.
A Practical VLAN Design
For a medium-sized office, a clean starting point might be:
- VLAN 10 — Management: Switch management IPs, out-of-band access. Tightly restricted.
- VLAN 20 — Servers: Internal servers, NAS, printers.
- VLAN 30 — Corporate WiFi: Authenticated employee wireless.
- VLAN 40 — Wired Clients: Standard desktop/laptop access.
- VLAN 100 — Guest WiFi: Internet-only, completely isolated from all other VLANs.
- VLAN 999 — Native/Black Hole: Unused native VLAN on trunk ports. No devices, no routing.
Keep VLAN IDs meaningful and consistent. Document them. A VLAN scheme that made sense to one engineer and was never documented is a source of pain that outlasts careers.
Voice VLANs
IP phones introduce an interesting case: a desk phone and a PC often share the same switch port (the PC is plugged into the phone's passthrough port). The phone needs to be in a Voice VLAN for QoS prioritisation; the PC needs to be in the data VLAN. Most managed switches handle this with a "voice VLAN" configuration on the access port — the port carries the data VLAN untagged (for the PC) and the voice VLAN tagged (for the phone). CDP/LLDP-MED tells the phone which VLAN to use.
Key Takeaways
VLANs create logical network segments on shared physical infrastructure. Access ports serve end devices in one VLAN; trunk ports carry multiple VLANs between network devices. Inter-VLAN routing requires Layer 3. Change your native VLAN. Design with intent and document everything — future you will be grateful.